What is the vulnerability being exploited
In cybersecurity, a vulnerability is a weakness that can be exploited by cybercriminals to gain unauthorized access to a computer system. After exploiting a vulnerability, a cyberattack can run malicious code, install malware and even steal sensitive data.
What are the 4 main types of security vulnerability?
- Network Vulnerabilities. These are issues with a network’s hardware or software that expose it to possible intrusion by an outside party. …
- Operating System Vulnerabilities. …
- Human Vulnerabilities. …
- Process Vulnerabilities.
What vulnerability means?
Vulnerability is the quality of being easily hurt or attacked. … Vulnerability comes from the Latin word for “wound,” vulnus. Vulnerability is the state of being open to injury, or appearing as if you are.
How vulnerabilities are exploited to launch an attack?
An exploit is a code purposely created by attackers to abuse or target a software vulnerability. … Once the exploit code is successfully executed, the malware drops a copy of itself into the vulnerable system. In some cases, an exploit can be used as part of a multi-component attack.What situation would be an example of an exploit?
An example of exploit is a journey to the top of a large mountain. Exploit is defined as to use someone or something to achieve one’s own purposes. An example of exploit is to pretend to befriend an intelligent student in class for the sole purpose of copying his homework.
What does exploiting others mean?
As a verb, exploit commonly means to selfishly take advantage of someone in order to profit from them or otherwise benefit oneself. … As a verb, exploit can also be used in a more neutral way that doesn’t imply selfishness: to make the best use of something, especially an opportunity, to create a profit or other benefit.
What are vulnerabilities in humans?
Vulnerability can be defined as susceptibility to a negative outcome or the state of being unprotected from some type of danger or harmful experience. People who are vulnerable may experience feelings of anxiety, fear, and apprehension due to the risk they experience for some type of harm.
What is vulnerability and risk?
Risk vs. threat vs. vulnerability. In a nutshell, risk is the potential for loss, damage or destruction of assets or data caused by a cyber threat. … And a vulnerability is a weakness in your infrastructure, networks or applications that potentially exposes you to threats.How do exploits relate to vulnerabilities?
As we’ve written before, a vulnerability is a weakness in a software system. And an exploit is an attack that leverages that vulnerability. So while vulnerable means there is theoretically a way to exploit something (i.e., a vulnerability exists), exploitable means that there is a definite path to doing so in the wild.
What are the factors of vulnerability?- Physical factors. e.g. poor design and construction of buildings, unregulated land use planning, etc. …
- Social factors. …
- Economic factors. …
- Environmental factors.
What are the types of exploit?
Exploits are commonly classified as one of two types: known or unknown. Known exploits have already been discovered by cybersecurity researchers. Whether the known exploit is due to a vulnerability in the software, OS, or even hardware, developers can code patches to plug the hole.
What do exploits do?
An exploit is a code that takes advantage of a software vulnerability or security flaw. … When used, exploits allow an intruder to remotely access a network and gain elevated privileges, or move deeper into the network. In some cases, an exploit can be used as part of a multi-component attack.
Why being vulnerable is important?
Being vulnerable can help us to work through our emotions easier (rather than pushing them away). Vulnerability fosters good emotional and mental health. Vulnerability also is a sign of courage. We become more resilient and brave when we embrace who we truly are and what we are feeling.
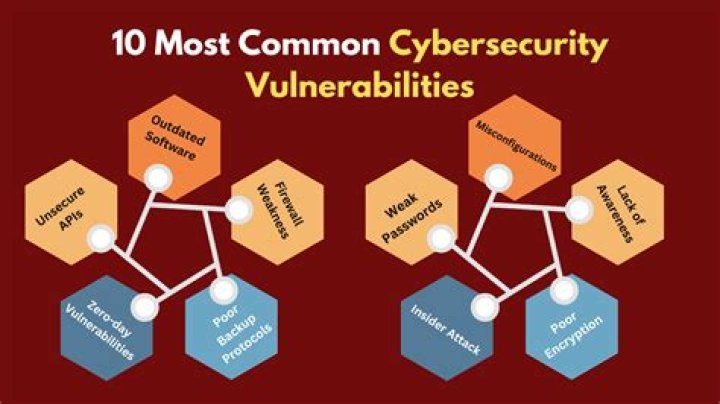
What are the types of vulnerability?
Types of vulnerability include social, cognitive, environmental, emotional or military. In relation to hazards and disasters, vulnerability is a concept that links the relationship that people have with their environment to social forces and institutions and the cultural values that sustain and contest them.
How do you know you are being exploited?
A classic sign you’re being exploited is when your paycheck arrives late — and repeatedly. If you’re exempt from overtime, being paid later than 30 days may actually violate your state’s labor laws. “Are you being paid at the same time every month?” asks Hegyi.
What does exploited person mean?
What does exploitation mean? Exploitation is the act of selfishly taking advantage of someone or a group of people in order to profit from them or otherwise benefit oneself. Exploitation is a noun form of the verb exploit, which commonly means to take advantage in such a way.
What does feeling exploited mean?
If you say that someone is exploiting you, you think that they are treating you unfairly by using your work or ideas and giving you very little in return.
Do all vulnerabilities have exploits?
Vulnerabilities can exist in everything from websites and servers to operating systems and software. An exploit is when a cybercriminal takes advantage of a vulnerability to gain unauthorized access. Not all vulnerabilities get exploited — but when they do, the resulting damages can be immense.
What's more important to focus on threats or vulnerabilities?
If you’re a left-handed soup sandwich, then the focus should be on vulnerabilities because the likelihood that you’ll be compromised by an advanced attack is low. …
What is the environmental vulnerability?
Environmental vulnerability is defined as a function of environmental exposure, sensitivity and adaptive capacity. … In addition to physical conditions and natural disasters, non-physical aspects such as population also affect the existence of environmental vulnerability.
How do you show vulnerability?
- Ask for what you need. When we’re hurting, it’s easy to dismiss our pain or try to protect ourselves and the people around us by closing off. …
- Be willing to expose your feelings. …
- Say what you want. …
- Express what you really think. …
- Slow down and be present.
What kinds of vulnerabilities might they exploit to cause harm?
- Computer Security vs. Cyber Threat.
- Malware.
- Unpatched Security Vulnerabilities.
- Hidden Backdoor Programs.
- Superuser/Admin Account Privileges.
- Automated Running of Scripts.
- Unknown Security Bugs.
- Phishing Attacks.
What is an example of an exploitative relationship?
In exploitative relationships, a partner will try to rush things along, moving at lightning speed to say “I love you” or move in together. That’s because the quicker they have your trust, the easier it will be to get what they want from you.
What could be done to limit the vulnerability?
- Inventory all devices connected to your network. Vulnerability assessments are useless without having an accurate accounting of what devices are connected to your network.
- Be vigilant in patching. …
- Train your employees to be a firewall.
Does the Bible say exploits?
The Bible declares, “The people that do know their God shall be strong, and do exploits.” That is a great promise and this is one of the most courageous verses in the Bible. Key Verse: Daniel 11:32b “… but the people that do know their God shall be strong, and do exploits.” (KJV).
What is an exploiter in Roblox?
An exploit is the use of glitches and software vulnerabilities in Roblox by a player to alter the game or gameplay for an unfair advantage. … Such exploits are not bannable by Roblox, but players caught doing this can be banned by a developer if the game has moderation infrastructure, like an admin script.
What is exploited host?
An exploited server is one that is no longer fully under your control. Someone else is using it for their own purposes. Common exploits are: To use the server to send out email (spam)
How does vulnerability affect our lives?
Vulnerability builds empathy and understanding It can feel terrifying to reveal our inner emotions, whether they are fear, shame, or hope. By allowing ourselves to be seen, we allow others to put themselves in our shoes. Vulnerability builds empathy and understanding for everyone involved.
What does it mean to be emotionally vulnerable?
What is emotional vulnerability? It’s the ability or willingness to acknowledge (and potentially express) one’s emotions. Particularly those emotions that are difficult or painful. Emotions such as shame, sadness, anxiety, insecurity, etc.
Is vulnerability a bad thing?
But, being vulnerable means something else when it’s placed in connection with human flourishing. … “Vulnerability isn’t good or bad. It’s not what we call a dark emotion, nor is it always a light, positive experience. Vulnerability is the core of all emotions and feelings.
What is defined as a weakness that can be exploited by attackers?
Explanation: Vulnerabilities is defined as the weakness in a system that can be exploited by cyber-criminals and attackers.



