What does an IDS that uses signature recognition use for identifying attacks
Detection method Signature-based IDS is the detection of attacks by looking for specific patterns, such as byte sequences in network traffic, or known malicious instruction sequences used by malware.
What IDS use signature recognition used to identify attacks?
Detection method Signature-based IDS is the detection of attacks by looking for specific patterns, such as byte sequences in network traffic, or known malicious instruction sequences used by malware.
Which of the following is the most common detection method used by IDS?
The two primary methods of detection are signature-based and anomaly-based. Any type of IDS (HIDS or NIDS) can detect attacks based on signatures, anomalies, or both. The HIDS monitors the network traffic reaching its NIC, and the NIDS monitors the traffic on the network.
How does signature-based intrusion detection system work?
It operates by using a pre-programmed list of known threats and their indicators of compromise (IOCs). … As a signature-based IDS monitors the packets traversing the network, it compares these packets to the database of known IOCs or attack signatures to flag any suspicious behavior.What are the two main types of IDS signatures?
Intrusion detection systems primarily use two key intrusion detection methods: signature-based intrusion detection and anomaly-based intrusion detection. Signature-based intrusion detection is designed to detect possible threats by comparing given network traffic and log data to existing attack patterns.
How does signature-based IDS differ from behavior based IDS?
This, broadly, is the difference between behaviour-based IDPS and signature-based IDPS. Signature-based IDPS is reactive, it can only respond once the crime has occurred. Signature-based IDPS relies on already defined behaviour that it has catalogued in its database.
What is ID signature?
A signature is a set of rules that an IDS and an IPS use to detect typical intrusive activity, such as DoS attacks. You can easily install signatures using IDS and IPS management software such as Cisco IDM. … As sensors scan network packets, they use signatures to detect known attacks and respond with predefined actions.
What are signature based attacks?
Signature-based ID systems detect intrusions by observing events and identifying patterns which match the signatures of known attacks. An attack signature defines the essential events required to perform the attack, and the order in which they must be performed.What is knowledge based IDS and signature based IDS?
A knowledge-based (or signature-based) IDS references a database of previous attack profiles and known system vulnerabilities to identify active intrusion attempts. Knowledge-based IDS is currently more common than behavior-based IDS. … It has lower false alarm rates than behavior-based IDS.
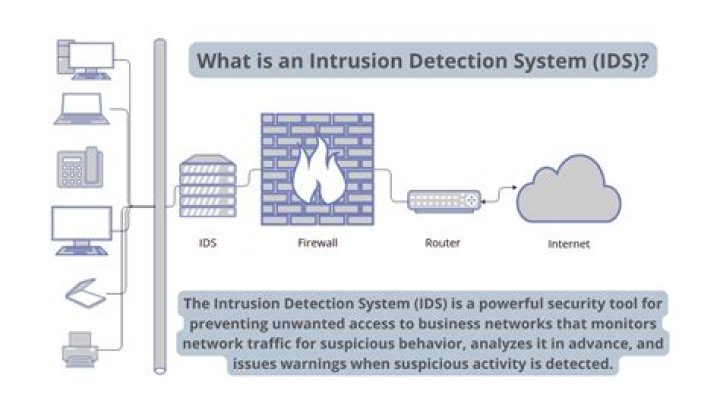
What is IDS in information security?An Intrusion Detection System (IDS) is a network security technology originally built for detecting vulnerability exploits against a target application or computer.
Article first time published onWhat are Intrusion Detection Systems IDS What IDS can do?
An intrusion detection system (IDS) is a device or software application that monitors a network for malicious activity or policy violations. … Some IDS’s are capable of responding to detected intrusion upon discovery. These are classified as intrusion prevention systems (IPS).
What are characteristics of signature based IDS?
52.What are characteristics of signature based IDS ?a.Most are based on simple pattern matching algorithmsb.It is programmed to interpret a certain series of packetsc.It models the normal usage of network as a noise characterizationd.Anything distinct from the noise is assumed to be intrusion activity
What's the difference between IDS and IPS?
The main difference between them is that IDS is a monitoring system, while IPS is a control system. IDS doesn’t alter the network packets in any way, whereas IPS prevents the packet from delivery based on the contents of the packet, much like how a firewall prevents traffic by IP address.
What is signature match detected?
Signature-based detection is a process where a unique identifier is established about a known threat so that the threat can be identified in the future. In the case of a virus scanner, it may be a unique pattern of code that attaches to a file, or it may be as simple as the hash of a known bad file.
How does a signature based IDS work quizlet?
How do signature-based systems work? Like antivirus, signatures are created and stored in a database – operations as well as binaries. If operations match a defined signature then an alarm is triggered.
What is signature in cyber security?
A signature, or digital signature, is a protocol showing that a message is authentic. From the hash of a given message, the signing process first generates a digital signature linked to the signing entity, using the entity’s private key.
What is signature in firewall?
The Web App Firewall signatures provide specific, configurable rules to simplify the task of protecting your websites against known attacks. A signature represents a pattern that is a component of a known attack on an operating system, web server, website, XML-based web service, or other resource.
What is a malware signature?
Many security products rely on file signatures in order to detect malware and other malicious files. The technique involves reading or scanning a file and testing to see if the file matches a set of predetermined attributes. These attributes are known as the malware’s ‘signature’.
What are the advantages and disadvantages of signature-based IDS?
Unlike anomaly detection systems, signature-based systems contain a preconfigured signature database and, therefore, can begin protecting the network immediately. The drawback to signature-based systems is their inability to detect new or previously unknown attacks.
What is the difference between signature-based detection and anomaly-based detection?
Signature-based and anomaly-based detections are the two main methods of identifying and alerting on threats. While signature-based detection is used for threats we know, anomaly-based detection is used for changes in behavior.
What is signature-based approach?
Thus each malicious executable signature contained only byte-sequences found in the malicious executable class. … To make the signature unique, the byte-sequences found in each example were concatenated together to form one signature.
What are the 3 types of IDS?
- Active and passive IDS. …
- Network Intrusion detection systems (NIDS) and Host Intrusion detection systems (HIDS) …
- Knowledge-based (Signature-based) IDS and behavior-based (Anomaly-based) IDS.
What are the different types of an IDS?
- Network intrusion detection system. …
- Host-based intrusion detection system. …
- Perimeter intrusion detection system. …
- VM-based intrusion detection system.
What is signature-based monitoring?
Signature-based detection is one of the most common techniques used to address software threats levelled at your computer. … This type of detection involves your antivirus having a predefined repository of static signatures (fingerprints) that represent known network threats.
Which is true of a signature-based IDS?
Which of the following is true of signature-based IDSes? Explanation: They are constantly updated with attack-definition files (signatures) that describe each type of known malicious activity. They then scan network traffic for packets that match the signatures, and then raise alerts to security administrators.
What is signature-based detection used in IDSS and IPSS )?
A signature-based IDS uses a library of signatures of known threats to identify them. An anomaly-based IDS builds a model of “normal” behavior of the protected system and reports on any deviations. A hybrid system uses both methods to identify potential threats.
What services are provided by an IDS?
An IDS is a passive monitoring device that detects potential threats and generates alerts, enabling security operations center (SOC) analysts or incident responders to investigate and respond to the potential incident.
What is an intrusion detection system when should this be used?
Intrusion detection systems are used to detect anomalies with the aim of catching hackers before they do real damage to a network. IDSes can be either network- or host-based. … Intrusion detection systems work by either looking for signatures of known attacks or deviations from normal activity.
What is intrusion detection and prevention?
Intrusion detection is the process of monitoring the events occurring in your network and analyzing them for signs of possible incidents, violations, or imminent threats to your security policies. Intrusion prevention is the process of performing intrusion detection and then stopping the detected incidents.
How does perimeter intrusion detection system work?
A PIDS typically acts as an early warning system, alerting a site’s alarm system while the intruder is still at the perimeter and not yet in a building or other interior area. … The two technologies work together, with PIDS providing early intrusion detection while cameras provide real-time assessment capabilities.
Why do we need IDS with IPS?
If an IPS is a control tool, then an IDS is a visibility tool. Intrusion Detection Systems sit off to the side of the network, monitoring traffic at many different points, and provide visibility into the security posture of the network. … In the hands of a security analyst, the IDS becomes a window into the network.