What are the most common NIST curves
As you can see, the most popular (preferred) elliptic curve is NIST P-256, followed by X25519.
What is the most commonly used curve defined by NIST?
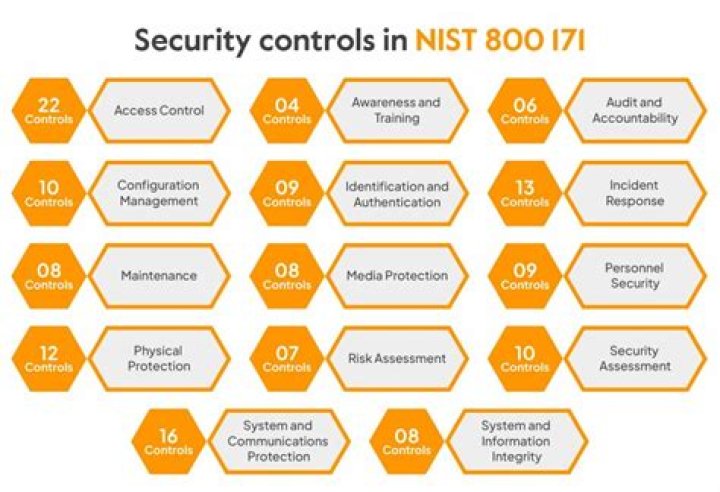
NIST has standardized elliptic curve cryptography for digital signature algorithms in FIPS 186 and for key establishment schemes in SP 800-56A. … In particular, comments were requested on the possibility of adding new elliptic curves to the current recommended set, as well as on digital signature schemes.
Is NIST P 256 Safe?
NIST curves like P-256 is generally not considered trustworthy, which is why the general consensus is to use Ed25519 for any elliptic curve cryptography.
What are NIST curves?
Definition. The NIST elliptic curves are a set of curves from the FIPS 186-3 standard that are recommended for US federal government use.In which of the following elliptical curves are used?
Elliptic curves are applicable for encryption, digital signatures, pseudo-random generators and other tasks. They are also used in several integer factorization algorithms that have applications in cryptography, such as Lenstra elliptic-curve factorization.
What is secp256r1?
secp256k1 is a pure SECG curve, while secp256r1 is a so-called NIST curve. NIST curves are more widely used and has received more scrutiny than other SECG curves.
Which curve is a popular publicly available alternative to NIST curves?
As you can see, the most popular (preferred) elliptic curve is NIST P-256, followed by X25519.
Why is ECC better than RSA?
The foremost benefit of ECC is that it’s simply stronger than RSA for key sizes in use today. The typical ECC key size of 256 bits is equivalent to a 3072-bit RSA key and 10,000 times stronger than a 2048-bit RSA key! To stay ahead of an attacker’s computing power, RSA keys must get longer.Does Bitcoin use Ecdsa?
In Bitcoin, the Elliptic Curve Digital Signature Algorithm (ECDSA) is used to verify bitcoin transactions1. ECDSA offers a variant of the Digital Signature Algorithm (DSA) [5] using the elliptic curve cryptography.
Is ECC more secure than RSA?ECC is more secure than RSA and is in its adaptive phase. Its usage is expected to scale up in the near future. RSA requires much bigger key lengths to implement encryption. ECC requires much shorter key lengths compared to RSA.
Article first time published onWhat is Ed25519?
Ed25519 is a public-key signature system with several attractive features: Fast single-signature verification. The software takes only 273364 cycles to verify a signature on Intel’s widely deployed Nehalem/Westmere lines of CPUs.
Is brainpool secure?
There are no security concerns in using the ECC Brainpool Curves, and there is some interest in using several of these curves in TLS 1.3. This document provides the necessary protocol mechanisms for using ECC Brainpool curves in TLS 1.3. This approach is not endorsed by the IETF.
Is secp256r1 secure?
The curves secp256r1 and secp256k1 have comparable security. If we consider only the best known attacks today, they have very close security. Both curves are defined over prime fields and have no known weakness, therefore the best attack that applies is Pollard’s Rho.
Which elliptic curve is used in Bitcoin?
Secp256k1 is the name of the elliptic curve used by Bitcoin to implement its public key cryptography. All points on this curve are valid Bitcoin public keys.
Is ECC asymmetric?
ECC is an approach — a set of algorithms for key generation, encryption and decryption — to doing asymmetric cryptography.
Where is ECC used?
ECC is among the most commonly used implementation techniques for digital signatures in cryptocurrencies. Both Bitcoin and Ethereum apply the Elliptic Curve Digital Signature Algorithm (ECDSA) specifically in signing transactions. However, ECC is not used only in cryptocurrencies.
Is ECC and Ecdsa same?
ECC is a mathematical equation taken on its own, but ECDSA is the algorithm that is applied to ECC to make it appropriate for security encryption.
Is Ecdsa quantum safe?
Symmetric ciphers (like AES-256, Twofish-256) are quantum-safe. Most popular public-key cryptosystems (like RSA, DSA, ECDSA, EdDSA, DHKE, ECDH, ElGamal) are quantum-broken! Most digital signature algorithms (like RSA, ECDSA, EdDSA) are quantum-broken!
What is Prime curve?
When computing the formula for the elliptic curve (y2 = x3 + ax + b), we use the same trick of rolling over numbers when we hit the maximum. If we pick the maximum to be a prime number, the elliptic curve is called a prime curve and has excellent cryptographic properties.
How many bytes is a Bitcoin signature?
Between December 2015 and early 2018, the signatures on the blockchain are nearly evenly split between 72 and 71 bytes in length. The 72-byte signatures have a low-s and a high-r value, which requires a prepended 0x00 byte.
What is nonce Mcq?
The nonce is the short form for Number Only Used Once is a number added to an encrypted block in a blockchain, which when rehashed, meets the difficulty level limitations. The nonce is the number that digital miners are solving for and when a solution is found, blockchain miners are awarded cryptocurrency in exchange.
What encryption does ethereum use?
Ethereum uses the Keccak-256 cryptographic hash function in many places. Keccak-256 was designed as a candidate for the SHA-3 Cryptographic Hash Function Competition held in 2007 by the National Institute of Science and Technology.
Is AES Elliptic Curve?
Short answer. The short answer is that the Elliptic Curve cryptography (ECC) OpenPGP keys are asymmetric keys (public and private key) whereas AES-256 works with a symmetric cipher (key).
Does TLS use SSL?
Transport Layer Security (TLS) is the successor protocol to SSL. TLS is an improved version of SSL. It works in much the same way as the SSL, using encryption to protect the transfer of data and information. The two terms are often used interchangeably in the industry although SSL is still widely used.
Why ECC is not widely used?
ECC uses a finite field, so even though elliptical curves themselves are relatively new, most of the math involved in taking a discrete logarithm over the field is much older. In fact, most of the algorithms used are relatively minor variants of factoring algorithms.
Is AES asymmetric or symmetric?
AES is a symmetric encryption algorithm because it uses one key to encrypt and decrypt information, whereas its counterpart, asymmetric encryption, uses a public key and a private key. Okay, let’s break that down.
Which is better ECC or non ECC memory?
At the cost of a little money and performance, ECC RAM is many times more reliable than non-ECC RAM. And when high-value data is involved, that increase in reliability is almost always going to be worth the small monetary and performance costs. In fact, anytime it is possible to do so, we would recommend using ECC RAM.
Is DSA safe?
DSA performed by experienced angiographers is a safe procedure that can provide critical diagnostic information.
Should I use Ed25519 or RSA?
Today, the RSA is the most widely used public-key algorithm for SSH key. But compared to Ed25519, it’s slower and even considered not safe if it’s generated with the key smaller than 2048-bit length. The Ed25519 public-key is compact. It only contains 68 characters, compared to RSA 3072 that has 544 characters.
Does SSH support Ed25519?
Technical overview. SSH can generate DSA, RSA, ECDSA and Ed25519 key pairs.
Does AWS support Ed25519?
Starting today, AWS customers can use ED25519 keys to prove their identity when connecting to EC2 instances. … EC2 customers can now also use ED25519 key pairs in addition to RSA based key pairs.