How do I authenticate users in Active Directory
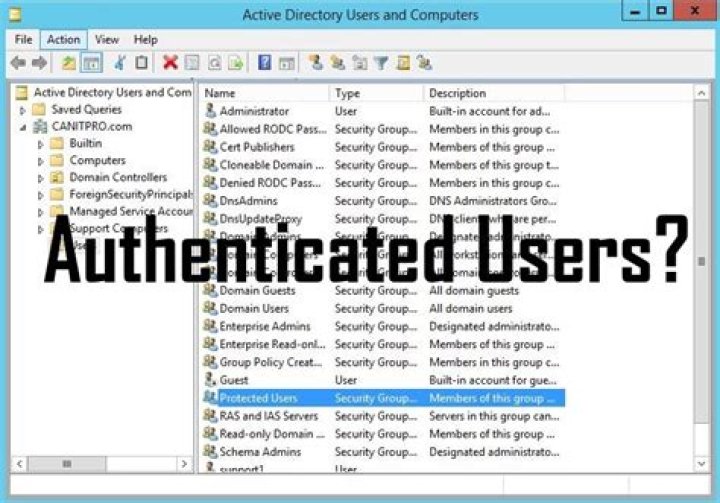
Select Authentication > Servers > Active Directory.Click Add. The Active Directory wizard appears.Click Next. The Domain Name page appears.In the Domain Name text box, specify the name of the Active Directory domain.
What is the best way to authenticate users?
- Biometric Authentication. Biometric authentication relies on the unique biological traits of a user in order to verify their identity. …
- QR Code. QR code authentication is typically used for user authentication and transaction validation. …
- SMS OTP. …
- Push Notification. …
- Behavioral Authentication.
What is the most common way to authenticate users?
Passwords are the most common methods of authentication. Passwords can be in the form of a string of letters, numbers, or special characters. To protect yourself you need to create strong passwords that include a combination of all possible options.
What is the authentication process in Active Directory?
The authentication process: The Endpoint Security client (1) requests an authentication ticket from the Active Directory server (2). The Active Directory server sends the ticket (3) to the client (1). The client sends the ticket to the Endpoint Security Management Server (4).How does domain controller authenticate users?
Users are authenticated in Windows Server 2003 environments by first locating a domain controller and then using the proper authentication protocol. The process is completely transparent to the user. The only thing the user has to do is provide a username and password.
What are the 5 factors of authentication?
- Knowledge Factors. Knowledge factors require the user to provide some data or information before they can access a secured system. …
- Possession Factors. …
- Inherence Factors. …
- Location Factors. …
- Behavior Factors.
How do you improve user authentication?
- Activate multifactor authentication functionality whenever possible for all of your accounts.
- Do not re-use your passwords. …
- Use single sign-on functionality combined with multifactor authentication in order to reduce the risk of account compromise.
- Use a password manager.
What are the three types of authentication?
Authentication factors can be classified into three groups: something you know: a password or personal identification number (PIN); something you have: a token, such as bank card; something you are: biometrics, such as fingerprints and voice recognition.What are user authentication credentials?
The credentials used in authentication are digital documents that associate the user’s identity to some form of proof of authenticity, such as a certificate, a password, or a PIN.
What is Active Directory password authentication?Azure Active Directory – Password Azure Active Directory Authentication is a mechanism of connecting to Microsoft Azure SQL Database by using identities in Azure Active Directory (Azure AD).
Article first time published onWhat are some authentication methods?
- Password authentication. …
- Two-factor authentication (2FA) …
- Token authentication. …
- Biometric authentication. …
- Transaction authentication. …
- Computer recognition authentication. …
- CAPTCHAs. …
- Single sign-on (SSO)
How do I know what type of authentication I have?
- Open the web application you would like to check.
- Open the developer tools. Press F12 if you are on Chrome.
- Open the “Network” Tab.
- Open an event.
- Check the “WWW-Authenticate” under the “Response Header” drop down. Basic:
What are three ways to digitally authenticate a user give an example of each way?
- Unique passwords. When most of us think of authentication, using a unique username and password combination likely comes to mind. …
- Preshared key (PSK). …
- Biometric authentication. …
- Two-factor authentication (2FA). …
- Behavioral authentication. …
- Device recognition.
How do you create a group by using Active Directory Users?
- Open the Active Directory Users and Computers console.
- In the navigation pane, select the container in which you want to store your group. …
- Click Action, click New, and then click Group.
- In the Group name text box, type the name for your new group.
Is domain controller same as Active Directory?
The main difference between Active Directory and Domain Controller is that Active Directory is a directory service developed for Windows domain networks while Domain controller is a server that runs on Active Directory Domain Service.
What is a member server?
Member server is a server role defined by Microsoft Active Directory (AD), a service that runs on the Windows 2000 and Windows Server 2003 operating systems. A member server belongs to a domain but is not the domain controller. … Member servers provide the backbone of services and applications in a domain.
What are the steps involved in an authentication process?
- The user enters a name and password. …
- The client sends the DN and password across the network.
- The server determines whether the password sent from the client matches the password stored for the entry with the DN sent from the client.
Which authentication method is strongest?
What is Beyond Identity? Beyond Identity combines two of the strongest authenticators: biometrics and asymmetric keys. It eliminates the password and provides an extremely secure authentication since the user’s identity is only stored locally on the device and it cannot be moved.
What is user authorization?
What Is Authorization? Authorization in system security is the process of giving the user permission to access a specific resource or function. This term is often used interchangeably with access control or client privilege.
What is strong user authentication?
Strong authentication is any method of verifying the identity of a user or device that is intrinsically stringent enough to ensure the security of the system it protects by withstanding any attacks it is likely to encounter.
How many types of authentication are there?
How Many Types of Authentication Are There? There are three basic types of authentication that we typically consider. The first is knowledge-based — you know something like a password or PIN code that only you, the identified user, would know.
What is an example of an authentication factor?
These factors include: Something you know, such as a password, passphrase or personal identification number (PIN) Something you have, such as a token or smartcard. Something you are, such as a biometric like a fingerprint.
How do I log into authentication?
- A client requests access to a protected resource.
- The Web server returns a dialog box that requests the user name and password.
- The client submits the user name and password to the server.
- The server validates the credentials and, if successful, returns the requested resource.
What are the three strategies that can be used to authenticate a user to a computer system?
There are three common factors used for authentication: Something you know (such as a password) Something you have (such as a smart card) Something you are (such as a fingerprint or other biometric method)
Which of the following is not a common criteria when authenticating users?
Common criteria when authenticating users include something you do, something you are, something you know, something you have, and somewhere you are. A person’s likes and dislikes are not common criteria; although, they may be asked as secondary questions when logging in to a system.
What is Active Directory universal authentication?
The Active Directory – Universal with MFA support is an interactive authentication method that supports Azure Multi-Factor Authentication, which provides a strong authentication with a range of easy verification options, and the user can choose the method that he prefers.
Is Active Directory an application?
Active Directory (AD) is Microsoft’s proprietary directory service. It runs on Windows Server and enables administrators to manage permissions and access to network resources. Active Directory stores data as objects. An object is a single element, such as a user, group, application or device such as a printer.
What is my SQL Server authentication username and password?
You can see the user mappings by opening Sql Server Management Studio and connecting to your server. In the Object Explorer area expand the Security and then Login folders (just under “Databases”). Double-click a login to open it’s Properties window, and find the User Mappings section.
What a user has?
A user often has a user account and is identified to the system by a username (or user name). Other terms for username include login name, screenname (or screen name), account name, nickname (or nick) and handle, which is derived from the identical citizens band radio term.
How do I authenticate a website?
- Check the connection type. You don’t have to be a pro to understand the website’s connection type. …
- Check the site’s security. …
- Check the URL. …
- Check website content. …
- Check the website’s social proof. …
- Google Safe Browsing Transparency Report.
Which of the following process is used for verifying the identity of a user?
The process of verifying the identity of a user is called Authentication.